Summary
- Nature of exploit: UniswapV3Callback functionality exploit
- Exploit Amount: $24,000 on the initial exploit, $1,100,000 on follow-up attacks
- Rescued Amount: $3,400,000 by a white hat hack
- Amount returned by exploiters: ~$800,000 as of the time of writing
- Final amount not rescued by the white hat hack or returned by exploiters: ~$300,000
- Thanks to the DAO proposal for PEP-07, a grant was given by the DAO to cover this amount.
Background: Augustus V6
ParaSwap uses a set of smart contracts known as AugustusSwapper to execute the best route calculated. These contracts decode the data provided to build a route the user can swap with on-chain.
As the DEX swapping field advances, ParaSwap has iterated the AugustusSwapper to provide better gas optimizations and swapping functions.
To provide a better trading experience for the user, the Augustus V6 smart contract was developed, which featured various improvements from its predecessor V5, including:
- Increased gas efficiency in swaps
- Additional checks to limit transaction-reverting errors
- Improved scalability for integration of new DEXes
Before its release, the Augustus V6 smart contract was audited by Hacken and Astrasec. Augustus V6 was announced on February 13th and released to the public on March 18th, following the auditors’ recommendations.
Following the public release of Augustus V6, one additional layer of security involved the ParaSwap DAO Bug Bounty program, hosted on the Hats Finance platform through which users can submit potential incidents to the DAO in exchange for a bounty.
Initial Vulnerability Report — MEV Attacks
On March 19th, David Benchimol, a lead engineer at Ironblocks, an end-to-end Web3 security provider automating proactive threat detection, submitted a report through the Hats Finance platform related to a front-running vulnerability impacting Permit2 swaps. ParaSwap took immediate action by removing its support from the UI and API and continuing to monitor the V6 contract behavior in real-time.
Shortly thereafter, a community member reported an unusual behavior on their wallet following an interaction with the Augustus V6 contract. Immediately after receiving the report, developers searched on-chain for similar cases, and the vulnerability was identified. This vulnerability had compromised 5 transactions, all of them through MEV attackers who had automatically exploited the funds. The total loss from these transactions equated to approximately $24,000.
The vulnerability was related to a specific function called uniswapV3SwapCallback(). It’s used as a callback to UniswapV3 direct functions, such as swapExactAmountInOnUniswapV3(). The purpose of these direct functions is to save gas on swaps by significant amounts; they’re basically a gas-optimized replacement to the native UniswapV3 Router. UniswapV3SwapCallback() is called back by a Uniswap pool, but it didn’t implement a proper caller check in some cases, which meant that an attacker could create a fake pool and call that function on behalf of the user in order to drain the tokens they approved for Augustus V6.
Any Uniswap V3 integrated network, such as Optimism, Arbitrum, Ethereum Mainnet, Base, Avalanche, BNB Smart Chain, and Polygon, would be affected.
Due to the nature of the exploit, it was concluded that it was a critical vulnerability and that any user who had approved the contract was exposed to it. To minimize the potential effects of the vulnerability, the team immediately deployed the mitigations outlined in the next section.
Mitigations and White Hat Rescue
The first action taken immediately after identifying the vulnerability was to stop the ParaSwap API for V6. By disabling the API, integrators that rely on it could not build transactions, reducing the exposure to people interacting and thus only affecting users who interacted between March 18th and 20th. In the main user interface, the swapping interface was reverted to Augustus V5.
Following this initial mitigation and in an effort to address the emergency situation as swiftly as possible, a group of security experts, including members from SEAL 911, Origin Protocol, Hats Finance, Conduit.xyz, and Ironblocks, among others, was assembled.
ParaSwap would especially like to thank 0xc0ffeebabe.eth and Daniel Von Fange from Origin Protocol and SEAL 911, who spent an entire night contributing significantly to the mitigation procedures. Additionally, we would also like to extend our thanks to Bogdan Habic and the Tenderly team, who assisted the mitigation team as well.
As the contract itself was not pausable, funds were still at risk of being drained. This led to the conclusion that the best course of action would be to conduct a white hat hack. The white hat hack would involve replicating the draining hack with the largest amount of addresses possible, thus moving the assets to a wallet where the funds could not be drained by a malicious actor.
The total amount of rescued funds equaled approximately $3,400,000, including ~$600,000 (10 WBTC) rescued by 0xc0ffeebabe.eth. With this operation now completed, the next step was to call the contract self-destruct function in the chains where it was available: Avalanche, BNB, and Polygon networks. The function could not be called on Ethereum Mainnet and Optimism due to the recent Dencun network upgrades.
With these measures now completed, the vulnerability was externally communicated to partners that had enabled V6 and users, requesting everyone to revoke the allowances to the contract immediately.
Follow-Up Exploiters
Following these communications, most of the funds that were currently exposed were secured. Despite the measures executed above, there was still an attack vector that could not be saved by the white hat hack on March 19th: if a user loaded a compromised address with approved assets before revoking the allowance, any malicious actor could drain these.
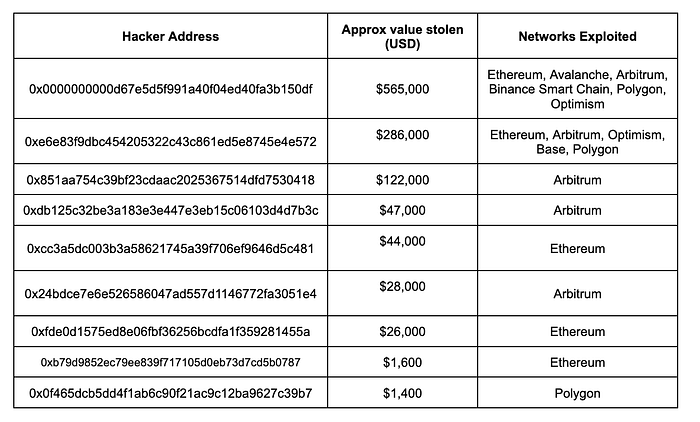
While many of these affected wallets revoked their allowances after the initial exploit, many were still affected despite our best communication efforts resulting in assets worth $1,100,000 being exploited using this vulnerability method.
Hacker Negotiation and Returns
Following the draining of funds from vulnerable addresses, security firms, and local authorities investigated the hackers identified above.
A set of on-chain messages was sent to different hackers with the following message, such as:
Hi, we are reaching out to you about a vulnerability you exploited on AugustusV6. We have taken immediate action by involving the appropriate authorities to investigate and facilitate the recovery of the misappropriated funds.
In the event that you exploited this vulnerability as a white or grey hat, we wanted to discuss the next steps. You can either email us at augustusV6@paraswap.org to discuss further, or transfer the funds directly to 0x66E90d840D7C4F3473E25dD8ca361747058c6Db0
If we do not hear back from you by Wednesday, March 27, 2024, 23:00 UTC we will assume you appropriated the funds with unlawful intent and we will pursue all criminal, legal, and administrative avenues available for the purpose of recovering the misappropriated funds.
Following these negotiations and other exploiters returning part of the funds, approximately ~$800,000 was returned from the original $1,100,000 exploited.
Return of Funds to Affected Users
As the aforementioned mitigations and communications with hackers took place, the process of return of assets secured by the white hat hack began. Transfers were made in batches, with the only requirement from the user being that they have revoked all permissions to the affected contract. This is an important step, as otherwise the funds could be exploited immediately after the deposit of funds.
While the return process for the white hat hack was ongoing, the ParaSwap Foundation put forward a DAO proposal outlining its plans to provide full refunds to affected users with a view to the long-term sustainability of the project.
The Foundation requested the DAO extend a grant to use the DAO’s ETH treasury to provide full refunds for affected users before April 4th. The initial requested amount was approximately ~$864,000 in ETH, but following further developments in the hacker negotiation front, this amount was reduced to ~$340,000.
Following a vote with 96.81% voting “for,” 103 ETH was granted to facilitate the process. This was transferred and converted to the tokens that were drained from users.
The first round of refunds using this grant was sent on Apr 14, 2024:
- Ethereum: https://etherscan.io/tx/0xeba56e080a5d51dcb3a9b166d2a9932a01719e83912c5c6544f72c5477aaf782
- Arbitrum: https://arbiscan.io/tx/0x28ee13ad202f842a8c7117fb038e99c34562bf7a2aa9ba54afcbce93fc306890
- Optimism: https://optimistic.etherscan.io/tx/0x86aa63617a9bf3f1c8cc0ad9d7dd32ed96478da443b0031a8234562b4f369c4e
- Base: https://basescan.org/tx/0xf6739b327caf27d8469085b84776478bd71848405c4880bddd9ff0b33dc957ee
- Polygon: https://polygonscan.com/tx/0x3908a5f6bae95a7f19313634f9fcb5c99fa16248f4dce398d68e5f05b69ff30a
- BNB: https://bscscan.com/tx/0x1b2660f11ed1fb953d89f795454e3c7b67a2ffed9821710796fb2ffe3eaa729c
All other returns, including the grant or the White Hat Hack, can be traced on-chain on each chain on the White Hat address: 0x66E90d840D7C4F3473E25dD8ca361747058c6Db0
Next Steps
Since ParaSwap launched in 2019, security has been the utmost priority for its users. This is the first vulnerability the project has encountered in its five years of smart contract releases.
Despite the mitigations implemented, this incident has shown that for ParaSwap to continue being the most secure interface for users, additional security commitments have to be made. This is why, before the re-launch of the V6 contracts, a set of security updates is being implemented to not only reduce the risk of a similar incident happening again but also ensure that ParaSwap emerges from this as the most secure aggregator in the space.
For the re-audits of the ParaSwap V6 contract, ParaSwap will increase the number of independent auditors from two to five. This will allow for more rigorous testing of the deployed smart contracts and for a higher number of security researchers to verify their safety.
About ParaSwap
ParaSwap is a leading DeFi middleware that unites the liquidity of decentralized exchanges into one protocol.
Our core mission is to drive DeFi participation to new heights by offering secure, efficient, and optimized trading solutions for individual traders and financial institutions to tap effortlessly into the fragmented liquidity pools.
